Table of Contents
The security lab has three subsystems that support research and teaching activities at the TU/e Mathematics and Computer Science department. The integration of the subsystems gives students and researchers an opportunity to investigate all kinds of security aspects.
Security Operation Center (SOC)
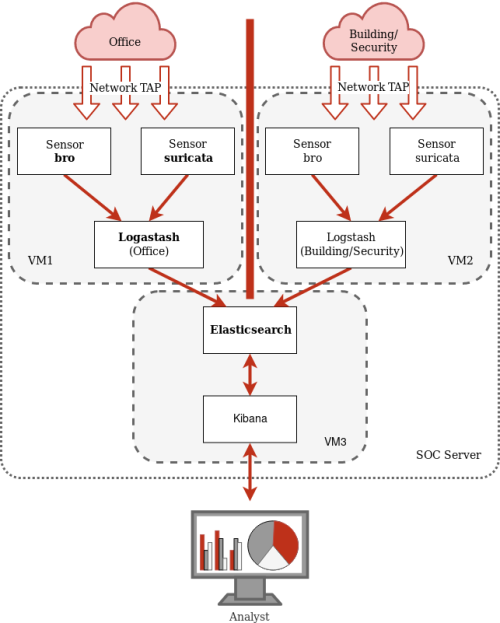
SOC is a centralized unit that monitors the security state of a computer network. In the lab, the initial scope of the SOC includes two areas to monitor: the IT network of the department (Office); the cyber-physical sensors network of the university (Building/Security). The following figure shows the schematic architecture of the SOC and an overview of the involved systems.
We allow students to conduct interesting experiment activities using the SOC. The activities include the followings:
- In 2IMS20 (Cyberattacks, Crime, and Defences course), students, as analysts, are assigned to detect and analyze suspicious events or attacks from the network traffic by reconstructing the evidence. The attacks were prepared in advance of the class. During the class, we inject the attacks into the monitored infrastructure of the SOC. This raises alerts along with other normal network traffic events. Students must reconstruct potential attacks by finding attack events from alerts. Furthermore, associated information of the attacks, such as victim and attacker IP addresses, has to be discovered by the students.
IoT Lab
The Security cluster IoT lab is a state-of-the-art facility designed to provide students with hands-on experience in developing and implementing security measures in IoT environments. The lab is equipped with several clusters of IoT devices, each with its own unique use case and automation. The IoT lab is designed with a distributed architecture, where different clusters of IoT devices are connected to the internet via a router. Each cluster consists of several IoT devices, such as sensors, cameras, and controllers, which are designed to perform specific tasks related to their use case. To provide automation and control for the IoT devices in the lab, the lab is also equipped with several smart home automation hubs, namely Amazon Echo, Samsung SmartThings, and Google Home Mini. These hubs allow students to interact with and control the various IoT devices in the lab using voice commands, mobile apps, or web-based interfaces. The IoT devices in the lab are connected to the smart home automation hubs using a variety of communication protocols, including Wi-Fi, Bluetooth, Zigbee, and Z-Wave. These protocols enable seamless communication and integration between the different IoT devices, as well as with the smart home automation hubs.

We have several IoT device clusters as shown in the figure. All the cluster actions are automated with one of the smart hubs.
Overall, the IoT lab is designed to provide students with a realistic and practical environment for learning about security in IoT environments. By connecting IoT devices to smart home automation hubs and the internet, students can explore the potential benefits and challenges of IoT technology, as well as develop their own security solutions for securing IoT devices and data.
The BlackHat's Lab (B-LAB)
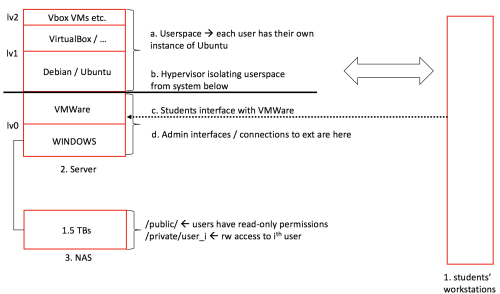
The B-LAB provides a powerful infrastructure to enable students and researchers alike to experiment with malware, vulnerabilities and exploits freely. The infrastructure is a setup to assure high isolation from the network environment while allowing remote collaboration from affiliate institutions.
The lab provides access to APT malware platforms, exploits and exploit kits traded in the underground, and nation-grade vulnerability exploits. All resources can be freely accessed in the context of the laboratory.
Current projects include:
- replication and evaluation of surveillance technology
- evaluation of exploit and malware resiliency in different operating conditions
- augmentation of exploit kits with new exploits and capabilities
- dynamic malware analysis
A schematic representation of the B-LAB's infrastructure is given below:
Lab access
Due to the content of the laboratory, access is on request only. The access procedure will be released shortly. In the meanwhile, you may contact Dr. Luca Allodi for additional information.
The laboratory is supported by the 4TU Federation .
.





